The risk modelling firm has developed its first probabilistic risk model for cyber-attacks, with contagious malware such as NotPetya a wildcard for future cyber catastrophes
Contagious malware attacks are the big new cyber threat, and have the scalability to produce a cyber catastrophe, according to risk modelling firm Risk Management Solutions (RMS).
RMS has developed its first probabilistic risk model for cyber-attacks. The firm ran an event in London on Tuesday to discuss its work on quantifying cyber risk.
Cloud outages ranked as the other type of attack most likely to cause a giant tail-risk cyber catastrophe.
That is despite most losses to date being caused by data losses and fraud.
Among risk managers, insurance buyers, and their insurance partners “there’s a lot of demand out there in the market,” said Andrew Coburn, senior vice president at RMS and director of the advisory board for the University of Cambridge’s Centre for Risk Studies.
“Although cyber for us is not one single model,” he said, referring to different methods and causes of losses.
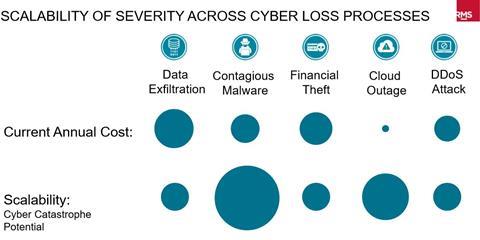
RMS splits cyber into five basic types of attack: data exfiltration; contagious malware; financial theft; cloud outage; and distributed denial of service (DDoS) attacks.
Data exfiltration has accounted for just over half of an estimated $2.3bn in cyber insurance claims over the past six years in the US market alone, according to RMS.
“Contagious malware is the new, up-and-coming candidate in this mix,” Coburn said.
WannaCry and NotPetya attacks caused about 300,000 infections in 150 countries.
RMS has been looking into “counterfactual downside scenarios” for the May 2017 WannaCry attack, which is estimated to have cost an $0.5bn economic loss.
An analyst stumbled across a “kill switch” to stop that malware attack; if no such kill switch had been found, RMS estimated a $3bn cost.
Some 85% of Windows v8 users were shielded by a Microsoft patch MS17-010 issued in March 2017.
If the malware had struck two months earlier than it did, infection rates and losses would have been much higher: $3-6bn, according to RMS.
NotPetya caused economic losses of $2.5-3bn and was a “destructive disk wiper” rather than ransomware, Coburn said, with no evidence that paying the ransom request led to any access to data being restored to victims.
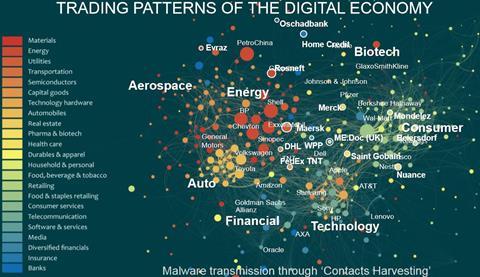
The contagious malware attack was 75% focused on Ukraine, with 2,000 infections in organisations across 65 countries being hit in total.
Spreading via financial exchange, it hit more than a dozen multinationals, Coburn noted, causing disruption to more than 30 international companies, and many more Ukrainian national organisations.
Global shipping firm Maersk was among the worst hit, losing 51% of devices on networks infected. Reinstallation across 45,000 machines took 10 days and cost the maritime firm a $450m loss.
“It shut down the shipping business across global ports…they had to return to pen and paper,” Coburn added.
Russian energy firm Rosneft also suffered 1% of devices on its network infected, for a $5m loss.
Insurers are putting pressure on their risk modellers to come up with answers for capital allocation, he emphasised.
That means assumptions about tail risk for extreme losses. So how big could a future contagious malware attack be?
“We’ve been looking at a potential cyber catastrophe, with not just 300,000 infections, but 3 million,” said Coburn.
In RMS Cyber Solutions v3, the firm has included scenarios running from one-in-ten-year cyber losses, all the way up to one-in-250-year potential catastrophes, for each of the five grouped types of cyber threat.
Cloud outages and contagious malware are both ranked high for cyber catastrophe potential, Coburn noted, despite historical data showing data exfiltration, denial of service and financial theft showing the biggest costs seen so far.
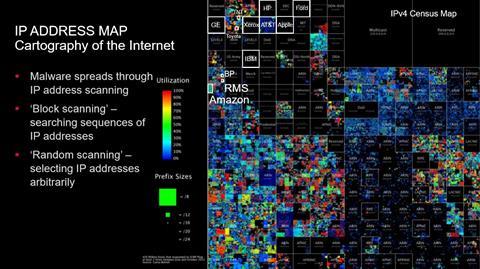
See below for three slides from Coburn’s presentation, showing, respectively: scalability of potential cyber catastrophes by attack type; the clustering and spread of cyber-attacks across sectors; and a grid map of IP addresses, showing how an attack targeting one firm could hit others on the same block.
















No comments yet