A lack of transparency on cyber attacks is benefitting the threat actors and increasing the threat
It was not long into the Covid-19 pandemic when they started. Text messages, emails, phone calls, all along the same lines. There’s been an unusual transaction on your account… we need to move funds to a new account… you’ve been awarded a tax rebate. And the solution was always the same. Move your funds, give us your details, let us in.
By no means were these communications new, or even unexpected. What was different, was the environment. This was a world of coronavirus, where money had suddenly become a lot tighter and the consequences of corporate inactivity could be significant.
And so, cyber-criminals watched as a comparative epidemic of its own arose, with the coronavirus pandemic acting as the spur towards a crime wave that will cost the world up to $6 trillion in 2021, according to Cybersecurity Ventures.
It might be, that only as few as one in five attempts at fraud were reported – a startling lack of openness about the true scale of the cyber-threat to the UK.
What is known is that the bad actors are both remarkably indiscriminate and carefully selective in their choice of targets. Indiscriminate in the sense that they are equally happy to target individuals and companies alike; selective in that when it comes to companies, they have a lot more opportunity to gain intelligence on their victims and be able to strike at exactly the right time.
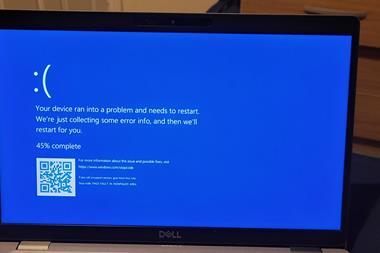
For corporates, Business Email Compromise and ransomware attacks make up a large proportion of the threat, and are certainly the most effective.
Perpetuating the cycle of fraud
This is where corporate risk, as a doctrine, currently finds itself: having to manage a situation that is worsened immeasurably by the current state of the world and the consequences of this – but also from the reaction by fellow companies to instances of compromise.
Which is to say, typically, no reaction. At least none that is public. In the majority of cases, attacks (and any resultant data breaches) are not reported – not to the authorities, the shareholders and certainly not to the customers.
Admitting a breach is embarrassing, and the risk of losing customers or share value is unacceptable – hence why so many are concealed.
But this also implies that ransoms are actually being paid to swiftly bring an end to the situation. Not only does this cast submissive companies as helping to perpetuate a cycle of fraud, but the suppression means that the sector cannot understand the true extent and nature of the threat and learn from the (genuine) mistakes of others.
Let us examine how these attacks occur, in order to see why this failure of communication is so important.
Exploiting human nature
With regards to Business Email Compromise, a bad actor will already have access to their victims’ internal system and will be able to intercept email traffic, being therefore able to monitor this for patterns and to identify the right time to strike – for instance, creating a fake invoice and sending a false email from the Director of Finance when this real individual is on holiday and will be unable to intercede in time.
Such an attack would take advantage of already existing vulnerabilities, at both the cyber and human level – with the latter being all too easily forgotten as a vector of compromise.
Similarly, ransomware attacks are predicated on both a cyber vulnerability (an inadequate defence system that will not prevent the ransomware from infecting computers) and a human vulnerability (for instance, clicking on the compromising link in the first place).
These kinds of attacks are doubly effective, and dangerous, because they can spread from one company to another very quickly and take advantage of trusted relationships.
What works at one company, will likely be successful at another: not only because those that work together have a more trusting relationship and thus communications are more likely to pass filters, but also because our psychologies are not so different.
Cyber-criminals employ behavioural psychology and profiling among their armory, devising methods of attack that rely on an understand of human behaviour just as much as they do electronic intrusion. Together, the two work in tandem to spread contagion in an extremely effective manner and, one would think, mandate that something appropriate is done.
Risk of re-infection
It is also important to note that, when a firm is hit once, it is likely to be hit again: a repeat attack from either the same source, knowing that the company is weak or paid the ransom, or from another acting on a ‘tip’ in the criminal underworld. Just as they do not select victims randomly, so too do they not leave the job undone.
The true extent of this is unknown due to the under-reporting. Organisations rarely publicise that they have been breached and adopt an ‘ostrich’ mentality.
Meanwhile, the bad actors are in dialogue over the Dark Web and learn about weaknesses and vulnerabilities, first-hand and the aggressive parties are by definition better-prepared than the defensive ones can ever be.
Notifying third parties and partners (not to mention the authorities) is critical to curb contagion, as all parties will be aware of the when and how of an attack and be better prepared to counter one themselves.
But it is not just a problem of outward-facing responsibility.
One action which is normally taken is to initiate an incident response program from an organisation’s IT team or external support, to provide recommendations that will mitigate the likelihood or consequences of a second breach. But, it has almost become common practice to ignore these recommendations based on cost grounds, or ‘it is unlikely to happen again’. This is an error. Failure to address the issues first-hand will likely result in re-infection.
The culture of silence needs to be broken so that organisations can understand just why this is such an epidemic of fraud.
The current climate of denial and obfuscation is fuelling the likelihood of severe cyber contagion between partner organisations and goes beyond simply being human error.
It is a cultural malaise which serves only to benefit the Threat Actors, who know that any target they may strike will be isolated by choice and without the support network that would come from a community that understood the breadth and depth of the threat and was cumulatively better prepared. It is no wonder that the severity of contagion is rising.
A successful management approach needs to be built on two pillars. Firstly, the culture of breach secrecy needs to be ended on the basis of shared knowledge being a benefit.
Break the stigma, forearm staff
If breaches are made public at every level and more people understood how and why they occurred, more could be done from a preventative position in the first place and the stigma would be lessened – and breached companies could alert their partners to the subsequent increased risk of contagion and help them to mitigate the potential impact.
Secondly, there needs to be greater understanding of how the threats arise not purely as a cyber concern but from the human side as well.
Through ill-prepared attitudes or well-meaning mistakes, a company’s weakest points may often be the employees: just as much time and effort needs to be spent in educating staff at all levels to identify the threats and have strict policies in place to mitigate them right from the start.
Corporate risk managers should therefore ensure that both sides of this coin are appropriately managed: maintaining constant and strong dialogue not only with the C-suite, but employees throughout the whole organisation.
Leadership on this matter must come from the top to highlight the importance of the matter at stake and to lead by example. Not only is every individual, and machine, a source of potential compromise, but what affects one organisation today could easily affect ten more tomorrow: the true face of contagion.
Transparency, responsibility and accountability offers the chance not only for companies to protect themselves from the cyber-threat, but to lead others in this crucial field.
Mary Nwaojei is head of cyber and information security, CEH, CISA, KCS Information Services.



















1 Readers' comment