It’s time for risk managers to hold cybersecurity vendors to account, says Richard Hollis, CEO of Risk Crew
New figures from Cybersecurity Ventures predict that cybercrime is going to cost the world economy $8 trillion by the end of this year.
These figures may surprise some cyber-novices but to industry veterans, they are the harsh reality of cybercrime today.

The cybercrime industry is now the world’s third-largest economy. This is because of the proliferation of tools available to launch attacks.
Twenty years ago, you needed to be a cyber expert, today you only need to own a computer.
Cybercrime enterprises have lowered the barrier to entry enabling anyone to launch attacks using their services. They lease the infrastructure; the amateur hacker launches the attack. Everyone’s a winner.
But to some organisations and risk managers, these worrying forecasts will leave them with many questions.#
”The cybercrime industry is now the world’s third-largest economy.”
Their spending on cyber increases year-on-year, their employee awareness grows every day, and they use every cyber defence tool recommended. So why does their risk not go down? Why does it increase?
Many government organisations say resilience can be improved through country-to-country collaboration. This is true. Countries should unite and share knowledge to build a more secure cyber world.
But it might also be wise to shine a spotlight on cybersecurity vendors and the important roles they must start playing in helping their customers achieve cyber resilience.
Especially the ones that earn billions every year, but never face the consequences of the breaches they don’t detect or stop.
The problems with the cybersecurity industry
It turns out, the biggest problem with cybersecurity all comes down to the industry itself.
Cybersecurity vendors make a lot of money from business insecurity, so do they ever want to fix the problem entirely? Regardless of their desires, they can’t.
As long as businesses use the internet, cybercrime is here to stay. But while vendors can’t abolish the problem, they can do more to contain it.
According to recent data, over 14 billion records have been compromised by cybercriminals in the last seven years alone and that’s just those reported from countries with mandatory disclosure legislation.
That’s more than twice the number of people walking on the face of this planet.
”If an organisation is breached because the security product they are using fails, the vendor holds no responsibility”
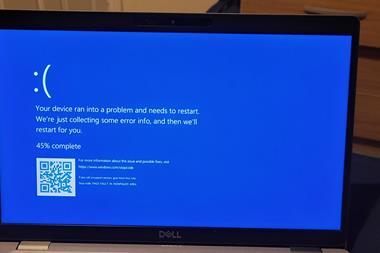
The reason for this is that cybersecurity product vendors have failed to keep pace with the skills, ingenuity, and adaptability of the threat actors of today. They are a step behind the threats when clearly, their job is to be a step ahead.
Then businesses purchase security products to secure their systems, but they continue to get breached, and one of the biggest problems all comes down to vendor accountability.
Product specifications and Service Level Agreements (SLAs) in the cybersecurity industry are specifically worded to ensure that vendors hold no responsibility when their product doesn’t perform properly or is associated with a breach.
This means if an organisation is breached because the security product they are using fails, the vendor holds no responsibility. But why is this acceptable? If the vendor holds no responsibility, what is their motivation in preventing attacks?
If businesses and risk managers really want to improve their cyber resilience, they must demand more accountability from security vendors. They must exercise their rights as consumers and ask for refunds when products fail or don’t perform as expected.
”If an organisation buys an anti-malware software solution and then suffers from a ransomware attack, it needs to hold the vendor accountable ”
When a company or consumer buys a product or service, they expect it to work. If it doesn’t, they will demand their money back. This is a practice that needs to transfer to the cybersecurity industry as well.
If an organisation buys an anti-malware software solution and then suffers from a ransomware attack, it needs to hold the vendor accountable so they have motivation to improve the product and stop successful ransomware attacks from occurring again in the future.
If they don’t do this, cyber resilience will be impossible because cyber defenders will always be on the back foot.
This is the only way to motivate vendors to stop attacks and make sure their products are capable of protecting businesses as cybercrime surges and offensive tools continue to innovate.
So, what can businesses and risk managers do?
It all comes down to asking the right questions of vendors before SLAs are agreed, contracts are signed, and tools are deployed: These questions include:
- What is your liability if your product fails or is determined to be the source of a breach?
- Will I get a refund if your product fails, is breached or is implicated in a security incident?
- Does your company use the product? If so, how and will you provide evidence and a point of contact I can speak with?
- Does the service provide remote connectivity to any other third parties? If so, will you provide details to include your liability in the event of a breach associated with this connectivity?
- Will you provide details on the company ownership and supply chain for this service for purposes of a risk assessment?
- Are service components subject to routine vulnerability assessment scanning and security penetration testing? If so, will you provide evidence?
- Were service software components subject to secure development procedures and testing? If so, will you provide evidence?
- Are service components subject to regular security patching?
- Has your company been breached in the last five years?
- Will you provide ten customer references?
If real cyber resilience is the goal, it’s time companies [and their risk managers] gave security vendors the motivation to do more.
They must be held accountable when things go wrong, it is their duty to keep businesses secure, and businesses have a duty to keep their customer’s data safe.
When businesses ask the right questions of vendors and ensure the products they are deploying can keep up to pace with today’s threat actors, cyber resilience will be possible.
Now is the time to put this into practice.


















No comments yet