Double extortion ransomware is on the rise, and risk managers should be worried. Chris Harris, EMEA technical associate vice president, data security at Thales, explores how to manage and mitigate these emerging threats
New global research from the Thales’ Data Threat Report revealed that 48% of IT professionals across the globe have reported an increase in ransomware attacks in the past year.
Despite this, not even half reported having a formal response plan prepared.
Unfortunately, for businesses globally, ransomware has become increasingly sophisticated in the past few years.
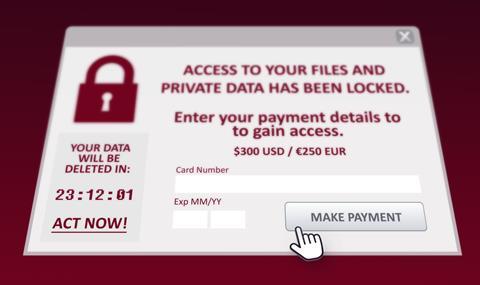
Cybercriminals have evolved their business models to include a second catastrophic phase in their technique: double extortion ransomware.
In other words, after compromising the victim’s sensitive data, the cybercriminal will then encrypt it, affording them the opportunity to demand two separate ransom payments – one to return the data, and one to decrypt it.
This puts even more pressure on victims to comply with cybercriminals’ demands.
What does this mean for risk managers?
Ransomware attacks are a multibillion-dollar crime, meaning they should be on the radar of all risk managers and the businesses they work for.
With data being a valuable commodity, any organisation, whether big or small, that is responsible for sensitive data or holds client, supplier, or partner information is therefore vulnerable to double extortion attacks.
This poses various challenges and financial implications. With the average ransom demands having soared between $50 million and $70 million, the potential monetary risks speak for themselves.
But once in criminals’ hands, ransomware gangs may also become aggressive and resort to triple extortion.
“Compromised data runs the risk of damaging relationships with formerly loyal customers and pushing them to the point of no return.”
In these cases, cybercriminals may divulge the data breach to the victim’s customers, revealing that their sensitive personal or financial data was accessed, and may even demand a secondary payment from customers whose data has been stolen.
With privacy and data security a top priority for many nowadays, revelations of this type create a wave of distrust and fury.
As a result, compromised data runs the risk of damaging relationships with formerly loyal customers and pushing them to the point of no return; it’s incredibly difficult to re-establish trust post-breach. Reputationally, the risks are immense.
Needless to say, the subsequent disruption caused by an attack if data has been deleted or damaged, can lead to further decreased productivity and financial losses.
For impacted organisations, it can also take considerable time to get back up and running and return to ‘business as usual’.
How to manage the threats
These attacks have become much more dangerous as they have evolved beyond basic security defences and business continuity measures like next-gen antivirus and backups.
However, perhaps more concerningly, there is a knowledge gap with many businesses not yet aware of these double and triple extortion ransomware tactics, let alone how they impact their data protection strategies.
The good news is there are various prevention and recovery tactics for double extortion ransomware that risks managers can adopt to manage and mitigate the risks.
These are:
-
Address the knowledge gap internally
With human error being a leading reason for attacks, anyone within an organisation may be the gateway for criminals to compromise data.
Risk managers must therefore invest in security awareness training to educate and familiarise all personnel with ransomware threats, including vectors such as phishing, social engineering, and how to recognise and securely handle sensitive data.
- Get wider business buy-in
Cybersecurity is a collective priority – that’s the only way breach attempts can be sufficiently prepared for or dealt with.
This includes response plan testing, fine-tuning as an ongoing board priority, and working collaboratively with IT and security teams to manage the threat.
-
Recognise the danger of outdated data protection strategies
With ransomware techniques, as well as the kinds of applications and data an organisation might be using, evolving at pace, strategies from even a couple of years ago may be out of date by now.
Continuously review, question, and evolve, rather than playing catch up.
-
Remember the Discover, Protect and Control paradigm
For ‘discover’, it’s absolutely critical to understand the whereabouts of your data.
In the first instance, conduct an expansive review of where your sensitive data is stored and how it is protected.
As per Thales’ Data Threat Report 2023, only 64% of European enterprises were ‘very confident’ or had complete knowledge of where their sensitive data was being stored.
-
Know your vulnerabilities, and act accordingly
For the ‘protect’ pillar, leverage vulnerability management programs to prioritise and address security vulnerabilities across your organisation that hostile actors could exploit.
This includes staying up to date with software patches, ensuring cloud storage is appropriately configured and secured, and making sure that more secure sign-on services like multi-factor authentication are turned on.
-
Be prepared
For the ‘control’ pillar, ensure your teams are properly prepared and resourced to securely build, deploy, and manage their systems with appropriate defences.
This also involves encrypting their most valued assets that they don’t want falling into the wrong hands.
When done correctly, this means that even if the attacker successfully exfiltrated sensitive data, it will be of no use to them without appropriate encryption keys.
On that note, also keep said encryption keys in secure, tamper-proof key management hardware so they cannot be extracted either.
-
Develop a ransomware recovery plan
Take the approach of ‘when, not if’, when it comes to the likelihood of a successful breach.
Organisations should be fine-tuning their ability to recover from an attack as quickly as possible.
Any good plan needs to cover not only the availability of your systems and data but also how to deal with the potential exfiltration and public exposure of that data.
-
If attacked, don’t instantly comply
All these degrees of extortion are driving the cost of ransomware up, with ransomware expenses projected to reach $265 billion by 2031.
While paying seems like a quick fix, it actually legitimises such ransom demands and encourages attackers to continue making them.
As a business is negotiating with criminals, there is no guarantee that even if they do pay up, their data will be restored to them.

















No comments yet